This function generates a JWT token (JSON Web Token) (according to RFC 7519).
The generated token is signed either with a certificate (parameter c) or an HMAC (parameter d).
JWT tokens consist of two JSON parts (header and payload). Both are passed to the function in a map (parameter b). See example.
As a result, the function returns the signed JWT token (with the three components header, payload and signature), encoded in Base64.
Parameters
Parameter | Description |
|---|---|
a | The JWT algorithm to be used (HS256, HS384, HS512, RS256, RS384, RS512, ES256, ES384, ES512, PS256, PS384, PS512). Note: Use the three dots to select a value. |
b | The name of the map with the JSON elements (header, payload). See example. |
c | ID of the local certificate (for JWT algorithms RSx, ESx, PSx in parameter a). |
d | Shared secret key (freely selectable) for HMAC signature (for JWT algorithmsHSx in parameter a). |
Examples
HMCA
First we fill the map mymap with the following entries. See function add to map(). Please note the special structure of the header key.
Key | Value |
|---|---|
@JWTHEADER_kid | 313476155373880299762899997753309067120 |
sub | 1234567890 |
name | John Doe |
iat | 1516239022 |
Now we use the function with the following parameters.
Parameter | Value |
|---|---|
a | HS256 |
b | mymap |
c | |
d | mysharedsecretkey |
This internally creates the following JWT structure.
Header: {"kid":"313476155373880299762899997753309067120","alg":"HS256","typ":"JWT"}Payload: {"sub":"1234567890","name":"John Doe","iat":1516239022} |
You can now check the validity of the generated JWT token (signed and Base64-encoded) with the function check JWT(). To do this, use the shared secret key from parameter d.
RSA
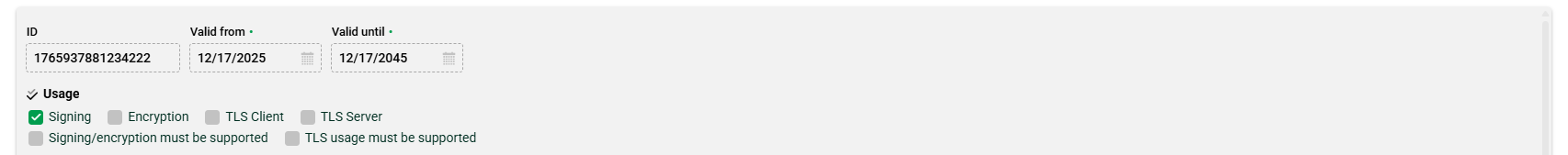
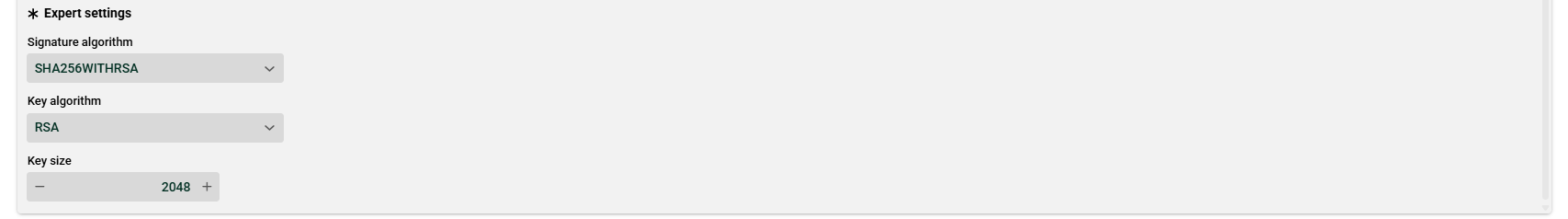
Certificate created on Lobster Data Platform:
Function parameters:
Parameter | Value |
|---|---|
a | RS256 |
b | mymap |
c | 1765937881234222 |
d |
Note on EC certificate generation
When using the Lobster Data Platform to create Elliptic Curve (EC) certificates, please be aware that the specific Named Curve cannot currently be selected within the configuration properties. The platform may default to a specific curve (such as NIST P-256) based on the key size provided.
Because different environments—such as blockchain applications, IoT devices, or specific TLS configurations—require exact curve specifications (e.g., secp256k1 vs. prime256v1) for interoperability, this default behavior might lead to compatibility issues. To ensure your certificate meets the precise requirements of your target system, we recommend generating your EC-based certificate and key using an external tool like OpenSSL—where the curve can be explicitly defined—and then importing it into the Lobster Data Platform.